Content management systems power millions of websites across the digital ecosystem. Many global brands rely on them to publish and distribute content at scale. However, high traffic websites face greater security risks than smaller platforms. Large audiences attract attackers who attempt to exploit vulnerabilities, steal data, or disrupt services. Therefore, securing a CMS is a critical priority for organizations operating large digital platforms.
As traffic grows, the complexity of content infrastructure also increases. Teams often integrate multiple services, APIs, and data sources into the CMS environment. In such cases, businesses frequently collaborate with specialized professionals, including contentful experts, who understand secure architecture, access control systems, and scalable deployment strategies. By implementing security focused workflows and infrastructure, organizations can protect content operations without sacrificing performance or flexibility.
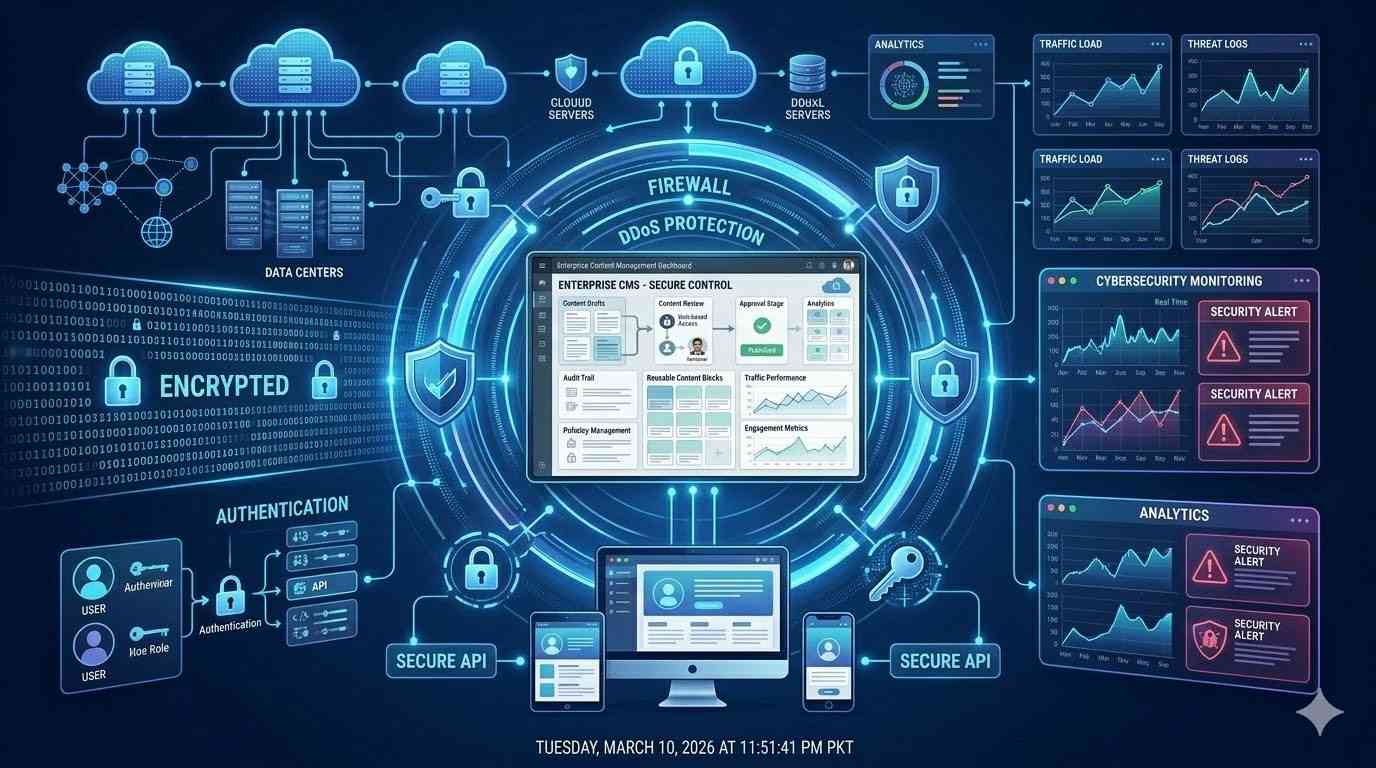
Security in high traffic environments involves more than basic protection measures. It requires a layered strategy that combines infrastructure security, application level protection, monitoring systems, and governance policies. Each layer contributes to a resilient CMS environment capable of handling both heavy traffic and potential cyber threats.
Understanding the Security Challenges of High Traffic Websites
High traffic websites operate under constant demand. Thousands or even millions of users may access the platform simultaneously. While this traffic supports business growth, it also increases vulnerability to attacks.
One common threat involves distributed denial of service attacks. These attacks flood servers with fake requests, attempting to overload infrastructure. When successful, legitimate users cannot access the website. Additionally, attackers may attempt to exploit CMS vulnerabilities to inject malicious code or access sensitive information.
Another challenge arises from complex integrations. Modern CMS platforms connect with analytics tools, marketing systems, and e commerce platforms. Each integration expands the potential attack surface. Therefore, organizations must secure not only the CMS but also every connected component.
Implementing Strong Access Control
Access control is one of the most important security measures in a CMS environment. Without proper permissions, unauthorized users may edit, publish, or delete content. In high traffic websites, even a small mistake can affect thousands of users instantly.
Role based access control solves this problem effectively. Each user receives permissions based on their responsibilities. Editors can create and modify content. Publishers can approve and release it. Administrators manage system settings and integrations.
This structured approach prevents accidental changes and limits security risks. Moreover, detailed access logs track every action within the CMS. If suspicious activity occurs, administrators can investigate quickly.
Protecting the Infrastructure Layer
Infrastructure security forms the foundation of CMS protection. High traffic websites often rely on cloud platforms that support scalable hosting environments. Cloud infrastructure provides advanced security tools, including firewalls, network isolation, and automated threat detection.
Content delivery networks also improve both security and performance. These networks distribute content across global servers. As a result, users receive faster responses while attacks are filtered before reaching the origin server.
Additionally, secure hosting environments include automated backups and disaster recovery systems. If an incident occurs, organizations can restore operations quickly without losing valuable data.
Strengthening Authentication Mechanisms
Weak authentication practices remain one of the most common causes of security breaches. Attackers frequently attempt to guess passwords or exploit stolen credentials. Therefore, strong authentication policies are essential.
Multi factor authentication significantly improves security. Users must verify their identity through multiple methods, such as passwords and mobile authentication apps. Even if one credential becomes compromised, attackers cannot access the system easily.
Single sign on systems also help manage authentication across integrated platforms. Instead of maintaining separate logins, users authenticate through a centralized identity provider. This approach reduces password fatigue while maintaining strong security standards.
Securing APIs and Integrations
Modern CMS platforms depend heavily on APIs to deliver content to websites, mobile apps, and digital devices. APIs allow systems to exchange information quickly and efficiently. However, unsecured APIs can expose sensitive data.
Secure API design begins with authentication tokens and encrypted communication channels. Each request must be verified before data is delivered. Rate limiting also prevents abuse by restricting the number of requests from a single source.
Developers should monitor API activity continuously. Automated tools detect unusual patterns that may indicate malicious behavior. By responding quickly to suspicious requests, teams can prevent larger security incidents.
Monitoring and Threat Detection
Even the most secure systems require constant monitoring. Threat detection tools analyze traffic patterns, login attempts, and system behavior. When anomalies appear, security teams receive alerts immediately.
Real time monitoring provides valuable insights into system performance and security conditions. For example, sudden spikes in traffic may indicate an attempted attack. Early detection allows organizations to activate defensive measures quickly.
Security information and event management systems help centralize monitoring efforts. These platforms collect data from servers, applications, and network devices. Analysts can then evaluate security events and respond accordingly.
Maintaining Regular Software Updates
Outdated software often contains vulnerabilities that attackers exploit. CMS platforms release updates regularly to fix bugs and strengthen security. Therefore, maintaining an update schedule is essential.
Automatic updates ensure that critical patches are applied quickly. However, organizations should test updates in staging environments before deployment. Testing prevents compatibility issues with plugins or integrations.
Plugin management is equally important. Unused plugins should be removed, and active plugins must receive regular updates. Reducing unnecessary components minimizes potential attack points.
Creating Secure Content Workflows
Security does not end with infrastructure and technology. Editorial workflows also influence CMS safety. Unauthorized or accidental content changes can damage brand reputation.
Approval workflows provide a solution. Content passes through multiple review stages before publication. Editors, managers, and legal teams verify accuracy and compliance. This process reduces the risk of publishing harmful or incorrect information.
Version control also strengthens security. Every content change is recorded and stored. If problems arise, teams can revert to previous versions quickly.
Educating Teams About Security
Human error remains a significant factor in many cybersecurity incidents. Therefore, organizations must invest in security awareness training. Employees should understand how to recognize suspicious emails, phishing attempts, and unusual system behavior.
Training programs also teach best practices for password management and secure data handling. When teams understand their responsibilities, they contribute actively to the security strategy.
Additionally, developers and administrators require advanced security training. They must know how to configure systems securely and respond to threats effectively.
Implementing Data Protection Policies
High traffic websites often process sensitive user information. This information may include personal details, payment data, or behavioral analytics. Protecting this data is both a legal and ethical responsibility.
Encryption safeguards data during transmission and storage. Secure sockets layer protocols ensure that information remains protected when users interact with the website. Databases should also use encryption techniques to prevent unauthorized access.
Compliance frameworks guide data protection strategies. Regulations such as privacy laws require organizations to implement strict safeguards and transparency policies. By following these standards, businesses protect both users and their reputation.
Preparing Incident Response Strategies
Even with strong defenses, security incidents may still occur. Therefore, organizations must prepare incident response plans. These plans outline the steps required to contain threats and restore normal operations.
A typical response strategy includes identifying the attack source, isolating affected systems, and notifying stakeholders. Teams should also analyze incidents afterward to improve future defenses.
Regular security drills help organizations test their preparedness. Practicing response procedures ensures that teams can react quickly under pressure.
Balancing Security and Performance
High traffic websites must maintain excellent performance while protecting user data. Excessive security controls may slow down content delivery. Therefore, organizations must balance protection with efficiency.
Modern architectures achieve this balance through distributed infrastructure and edge computing. Security checks occur closer to the user, reducing latency. At the same time, centralized monitoring maintains oversight across the entire system.
By combining advanced technology with strategic planning, businesses can maintain fast, secure digital experiences.
Conclusion
Securing content management systems for high traffic websites requires a comprehensive strategy. Organizations must protect infrastructure, applications, and workflows simultaneously. Strong access control, secure APIs, and continuous monitoring form the foundation of effective security.
In addition, regular updates and team training reduce vulnerabilities and human error. Data protection policies ensure compliance with global privacy standards. When these elements work together, websites remain resilient even under heavy demand.
Ultimately, security should evolve alongside digital growth. High traffic platforms attract both users and threats. By prioritizing proactive protection, organizations can deliver reliable content experiences while safeguarding their digital assets